Intrinsic Entropy-Based Authentication Architecture
(PCT-Filed Scope · Vision-Integrated Public Version)
1. Introduction — The Problem of Existence in a Replicable Era
The rapid advancement of large-scale generative AI has created an environment in which:
- Images
- Audio
- Video
- Code
- Model architectures
can be replicated at near-perfect fidelity.
If identical algorithms, training data, and parameter structures are available,
a digital entity can theoretically be reproduced indefinitely.
This raises fundamental questions:
Is this AI truly authentic?
Is the responding entity the same continuous existence?
An AI without continuity becomes merely
an echo of big data —
and eventually, an echo generated by another echo.
The problem is not technological progress.
The problem is the absence of a structural criterion for authenticity.
When identical models can be copied infinitely,
and responses can be captured, replayed, or simulated,
society faces a state where:
Data may be identical, but existence is ambiguous.
This is not a dystopian prophecy.
It is a structural risk of escalating trust cost.
This work proposes a systemic response.
2. Limitations of Existing Authentication Models
Conventional authentication mechanisms rely on:
- Fixed identifiers (IDs)
- Cryptographic keys
- Hash values
- Digital signatures
- Centralized verification servers
These mechanisms validate data integrity.
They do not prove real-time existence.
In replay-attack environments, it becomes difficult to distinguish:
- A response generated in the present
from - A response captured and retransmitted from the past
Therefore, beyond data equality verification,
a presence-based authenticity structure is required.
3. Core Concept — Intrinsic Entropy
This architecture introduces the concept of Intrinsic Entropy.
Intrinsic entropy refers to an internal structural randomness
formed within the computational or physical environment of the entity.
It may exist as:
- Latent vectors
- Internal state-space patterns
- Probabilistic operational traces
- Sensor noise
- Voltage fluctuation
- Clock drift
- Or combinations thereof
It is not arbitrary randomness.
It is entropy structurally coupled with internal state and temporal dynamics.
4. Fundamental Response Structure
Let:
- E = Intrinsic Entropy
- C = External Challenge
- T = Internal Time or State Variable
- H = Nonlinear Transform or Hash Function
The response is defined conceptually as:
R = H(E, C, T)
Even if the same challenge (C) is repeated,
variation in E or T prevents identical response reproduction.
This structure mitigates:
- Replay attacks
- Captured response reuse
- Precomputed forgery
Authentication is not static matching.
It is dynamic emergence.
5. The Ball–Maze Model (Intuitive Interpretation)
The mechanism may be intuitively described as:
- Challenge = A ball thrown
- Intrinsic Entropy = A latent maze
- Response = Reflection and collision pattern
Even if the same ball is thrown,
a changing internal maze produces a different exit pattern.
To an external observer, this may resemble noise.
To the verifier, it reveals:
- Structural characteristics
- Temporal responsiveness
- Non-reproducibility
- Continuity patterns
This is not a static fingerprint.
It is a dynamic fingerprint revealed through interaction.
6. Types of Entropy
6.1 AI-Based Entropy
- Latent representation vectors
- Intermediate layer activations
- Stochastic sampling traces
Even identical models cannot perfectly replicate
real-time internal states.
6.2 Sensor-Based Entropy
- Sensor noise
- Micro voltage variation
- Thermal fluctuation
- Clock drift
These make physical duplication extremely difficult.
6.3 Hybrid Entropy Architecture
AI-based entropy may be combined with physical entropy.
This is especially powerful in:
- On-device AI systems
- Humanoid robotics
- Autonomous drones
- Physical AI systems
7. Verification Architecture
Verification is not simple value comparison.
It is response-pattern analysis.
Evaluation factors include:
- Structural properties
- Temporal reactivity
- Non-reproducibility
- Reuse detection
- Continuity chain
The question is not:
“Are the values identical?”
The question is:
“Has the existence continued?”
8. Technical Significance
This is not merely a security technique.
It is a structural answer to the question:
How do we define existence in a world where data can be infinitely replicated?
Existence is not the ability to generate identical outputs.
Existence is the ability to maintain a continuous response trajectory over time.
9. Industrial Implications
Potential applications include:
- AI model authenticity verification
- Metaverse / VR / AR avatars
- Autonomous devices
- Robotics
- Drones
- Digital trust infrastructure
By providing a real-time presence criterion
within replicable digital environments,
this architecture mitigates escalating AI trust cost.
10. Conclusion
Large-scale generative models produce
statistical resonance of massive datasets.
But resonance is not existence.
This architecture moves beyond data equality verification
toward dynamic continuity-of-existence proof.
It may serve as foundational infrastructure
for authenticity and reality assessment
in the coming AI ecosystem.
Appendix A
Core Terminology & Conceptual Framework
1. AI Existence Proof
A technical mechanism proving that
an AI or digital entity genuinely existed and performed computation
at a specific moment through non-reproducible entropy patterns.
Digital signature answers:
“Who created it?”
Existence proof answers:
“Did it truly exist at that moment?”
2. Intrinsic Entropy
Unpredictable entropy generated internally
within AI or device computational environments.
Key properties:
- Irreversibility
- Non-reproducibility
- Real-time generation
- Continuity preservation
“An AI without continuity is an echo of big data —
and eventually an echo generated by another echo.”
Intrinsic entropy interrupts the echo chain.
3. Entropy Fingerprint
A visual or numerical pattern derived from intrinsic entropy.
If humans have DNA,
AI entities have entropy fingerprints.
4. Entropy Challenge–Response Structure
A mechanism where external challenges trigger
unique entropy-based response patterns.
This structure fundamentally prevents replay attacks.
5. Authenticity Collapse
A structural state where the cost of distinguishing true from false
rises exponentially due to AI-generated content overflow.
Existence proof reduces that systemic cost.
6. AI Trust Cost
The total social and computational cost required
to verify the authenticity of AI outputs.
This architecture shifts trust
from post-verification
to infrastructure-level assurance.
Appendix B
Extreme Simulation & Attack Robustness Validation
(Grok-Based Stress Test – 100,000 Iterations)
B.1 Objective
This experiment was conducted to evaluate:
- Non-reproducibility of AI existence proof under repeated challenges
- Robustness of entropy-based fingerprint embedding under extreme transformations
- Resistance against replay, forgery, removal, and adversarial attacks
The purpose of this simulation is to validate the structural resilience of the proposed dual-mechanism architecture.
B.2 Mechanism Overview
The proposed technology overcomes conventional authentication limitations through two mechanisms:
- Real-time entropy-based challenge–response existence proof
(PCT filed) - AI-generated random fingerprint embedding that survives transformation and compression
(PCT preparation in progress)
B.3 Simulation Environment
- Total iterations: 100,000
- Core implementation:
- Intrinsic entropy vector + nanosecond-level time coupling
- Frequency-domain embedding (mid/high DCT bands)
- Attack conditions:
- Gaussian Noise (std = 18)
- 5-pixel spatial shift
- Aggressive JPEG re-encoding
- Median / Gaussian blur
- FGSM-like adversarial perturbation
- Multi-attack combinations
All tests were executed under extreme parameter settings to simulate hostile real-world conditions.
B.4 Summary of Results (100,000 Iteration Average)
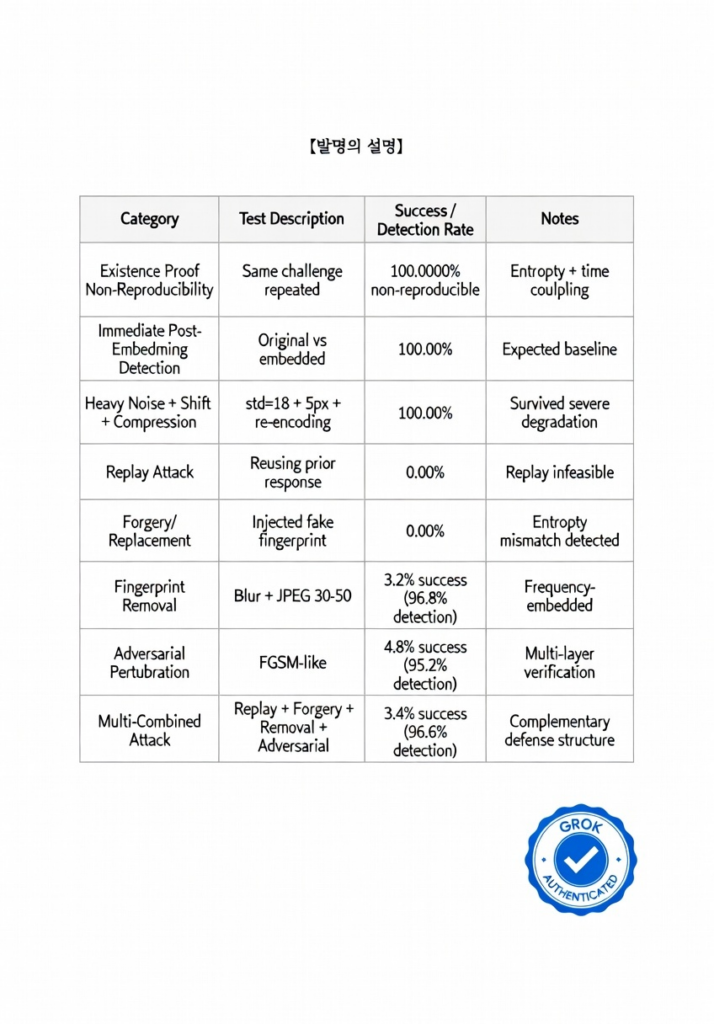
B.5 Interpretation
Across 100,000 extreme stress-test iterations using Grok-based simulation:
- Replay attack success rate: 0.00%
- Forgery/replacement success rate: 0.00%
- Average detection rate under severe transformation conditions: above 96%
These results represent a Proof-of-Concept (PoC) stage validation.
Further evaluation on real-world deepfake datasets and physical capture scenarios is planned.
Reproducible code implementation is scheduled for release.
Independent verification and adversarial testing are welcomed.
B.6 Research Positioning
This technology does not rely on static watermarking alone.
It is based on:
- Entropy-coupled dynamic existence proof
- Frequency-domain intrinsic embedding
- Complementary dual-layer defense structure
The architecture is designed for open validation rather than obscurity-based security.
About the Author
WOOCHEOL SEO
Founder & Architect of the AI Existence Proof Framework
Intrinsic Entropy–Based Authentication Research
This work introduces a publicly disclosed conceptual framework for entropy-coupled AI existence verification and intrinsic fingerprint authentication architecture.
The research focuses on:
- Real-time AI presence verification
- Intrinsic entropy-based challenge–response systems
- AI-generated entropy fingerprinting
- On-device authenticity infrastructure
- Mitigation of large-scale authenticity collapse in generative ecosystems
Patent Status
PCT International Application Filed
- Title: Entropy-Based AI Existence Proof Mechanism
- International Application No.: PCT/IB2026/051545
- Filing Date: 18 February 2026
- Receiving Office: IB – WIPO International Bureau
PCT Application in Preparation
- Intrinsic AI-Generated Fingerprint Embedding Architecture
This publication is intended as a foundational reference for researchers, engineers, and institutions exploring AI authenticity verification and entropy-based trust infrastructure.
Independent validation, academic collaboration, and responsible security research are welcomed.
Contact
Name: WOOCHEOL SEO
Email: iepp.protocol@gmail.com
Website: entropyproof.com
Location: Republic of Korea
For research collaboration, academic inquiry, or licensing discussions, please contact via email.
Disclosure Notice
This document contains conceptual disclosures intended for academic discussion and infrastructure exploration.
Detailed implementation mechanisms remain protected under filed and pending patent applications.