Entropy Lineage & TRP Hardness
0. Philosophical Foundation — Identity as Continuity
The Ship of Theseus — Interpreted through IEPP
Even if every component of a ship is replaced,
if the ship has continuously moved along the same trajectory,
we still call that ship the “Ship of Theseus.”
Conversely,
even if another ship is constructed using identical components,
if that ship has not followed the continuous trajectory of the original ship,
it is not the Ship of Theseus.
IEPP identity follows this principle.
The physical sameness of an object (code, weights, memory state) is not the fundamental property of identity.
Only the continuity of state transitions through time — the canonical lineage — establishes identity.
Therefore,
identity is not a static attribute contained inside an object,
but a property that emerges from continuous state evolution over time.
IEPP provides a structure to verify this continuity.
1. Core Conclusion
IEPP is not a static key-based authentication system.
IEPP is a trajectory continuity-based existence proof mechanism.
Instead of proving possession of a static secret, IEPP verifies that an entity has continuously evolved from prior states.
The structure combines:
intrinsic entropy
challenge-response binding
state continuity linkage
canonical lineage comparison
Observed properties:
even if a clone shares the same prefix trajectory,
the canonical trajectory diverges immediately after fork
the canonical continuation cannot be reproduced exactly.
2. IEPP Entropy Lineage Structure
IEPP responses are generated from the combination of:
E = intrinsic entropy
C = external challenge
T = time
S = continuity state
General form:Ri=H(Ei∥Ci∥Ti∥Si)
Intrinsic entropy is not artificially generated randomness.
It is measured from naturally occurring variability in the execution environment.
Examples:
timing jitter
floating point rounding variation
runtime latency fluctuation
OS randomness source
hardware level noise
These sources introduce variability that makes exact state replication difficult.
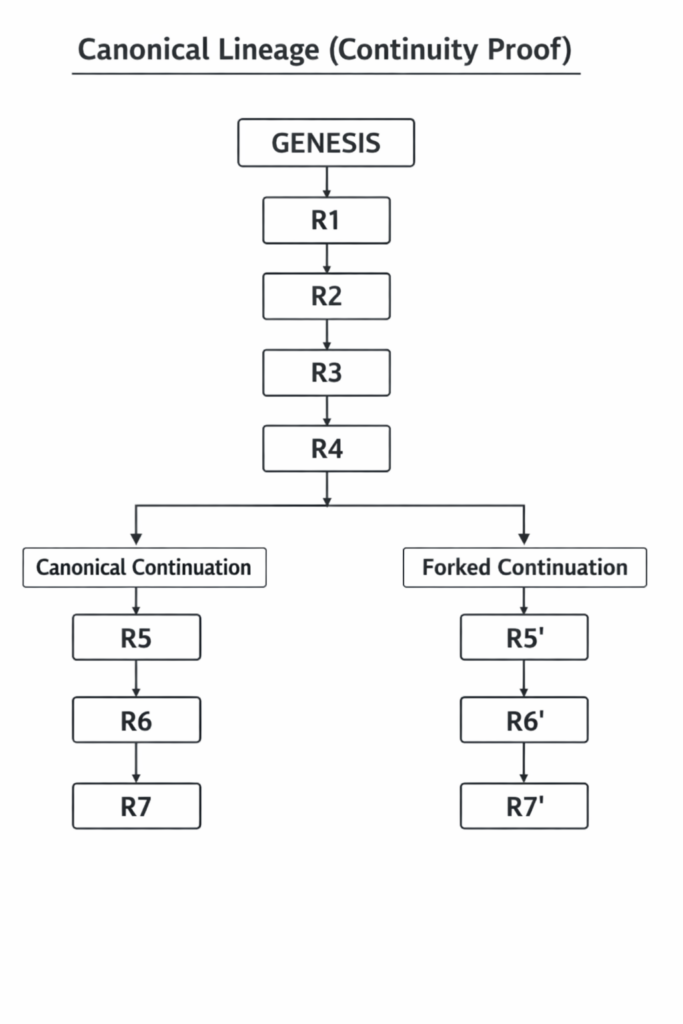
3. Canonical Lineage Model
IEPP defines identity as a trajectory rather than a single value.
Canonical lineage:
GENESIS → R1 → R2 → R3 → R4 → R5 → …
Fork example:
GENESIS → R1 → R2 → R3 → R4
├─ R5 (canonical)
└─ R5′ (clone)
Observation:
divergence occurs immediately after fork.
Identity is defined by continuity of trajectory, not by structural similarity of components.
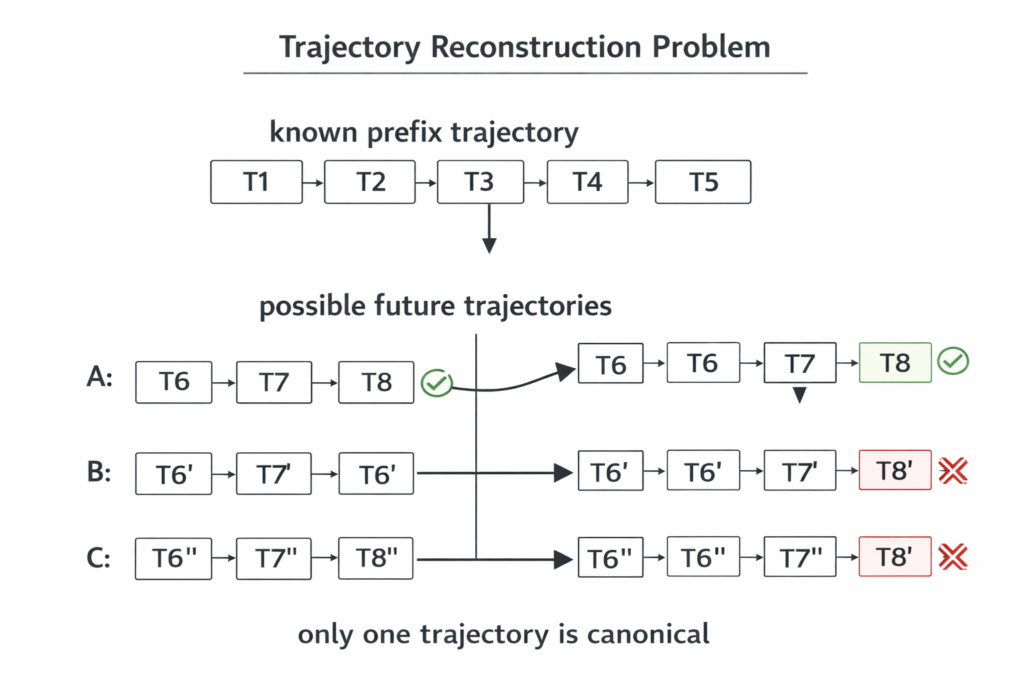
4. TRP — Trajectory Reconstruction Problem
TRP studies the following question:
Given a prefix trajectory, can the canonical continuation be reproduced?
We adopt the following hypothesis.
TRP Hardness (One-line Definition)
Pr[Tclone(k+1:n)=Tcanonical(k+1:n)∣T1:k]≤ε(n−k)
Interpretation:
Even if an attacker knows the full prefix trajectory,
the probability of reproducing the canonical continuation becomes negligibly small.
This implies:
post-fork canonical lineage is computationally difficult to predict.
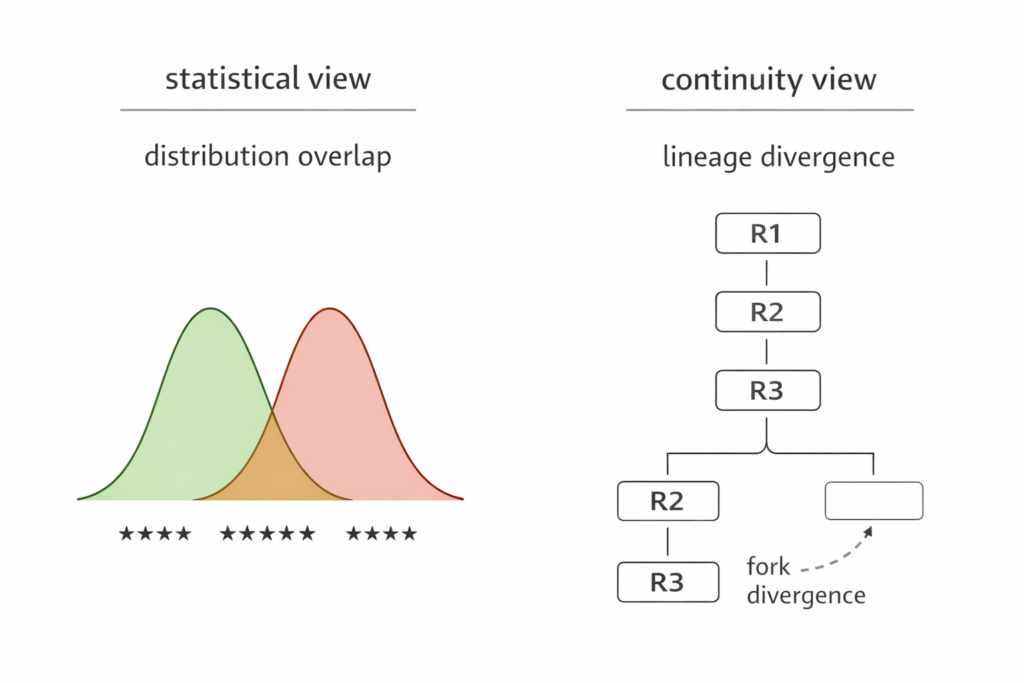
5. Experimental Observations
5.1 lineage continuity experiment
Observed behavior:
immediate divergence after fork
canonical lineage remains internally consistent
fork lineage diverges at first step after fork
fork match rate ≈ 0%
5.2 attacker model experiment
Assumptions:
attacker knows algorithm structure
attacker knows challenge values
attacker knows previous responses
attack attempts:
replay last response
replay random previous response
modify challenge
guess secret
seed-based imitation
Results:
attack success rate = 0%
replay attempts detected
forged fingerprints rejected
5.3 entropy source substitution experiment
Entropy sources tested:
os.urandom
python random
numpy random
torch random
mixed entropy
Result:
fingerprint uniqueness remained 100%.
The system does not rely on a single entropy generator.
5.4 physical-like entropy experiment
Entropy sources simulating real-world variability:
timing jitter
floating point noise
runtime latency variation
Result:
entropy uniqueness remained 100%
fingerprint uniqueness remained 100%
Indicates that intrinsic entropy sources may exist in typical runtime environments.
6. Interpretation
Observed properties suggest:
each response is difficult to reproduce exactly
trajectory continuity is difficult to forge
clone trajectories separate from canonical lineage
behavior persists across entropy source variations
IEPP may provide a structure for trajectory-based identity.
Identity is represented as continuity rather than static equivalence.
7. Importance of Real-World Validation
Current experiments were conducted in controlled environments:
Colab runtime
CPU environments
simulated entropy sources
simulated attacker models
These results represent early-stage logical validation.
Real-world environments introduce additional entropy sources:
hardware timing jitter
CPU execution variability
GPU computation characteristics
OS scheduling behavior
memory access variation
thermal fluctuation
power state changes
system load variation
Further experimental validation is important across:
different hardware environments
different operating systems
mobile devices
edge devices
virtualized environments
long-duration runtime conditions
IEPP evaluation differs from deterministic systems.
The primary evaluation objective is not identical reproducibility.
Instead, the key observation is consistent divergence after fork.
IEPP validation therefore focuses on trajectory divergence consistency.
8. Limitations and Open Questions
TRP hardness currently relies on empirical observation.
Further research directions include:
formal complexity analysis of TRP
modeling entropy sources
canonical lineage governance models
distributed verification approaches
improved statistical distance metrics
long-duration real-world testing
IEPP proposes identity defined through continuity of state evolution.
This perspective differs from traditional static identity approaches.
Figure placement summary
Figure 1
Canonical lineage diagram
INSERT in Section 3
Figure 2
Statistical similarity vs continuity difference
INSERT in Section 5.1
Figure 3
TRP conceptual diagram
INSERT in Section 4