Policy & Deployment Proposal for Trajectory-Based Identity
1. Purpose of the Policy Layer
IEPP is not intended to function solely as a cryptographic primitive.
It is designed as an infrastructure component capable of supporting identity continuity for:
AI agents
avatars
digital entities
autonomous systems
digital assets
As AI systems become capable of replication, migration, and continuous self-modification, identity can no longer be defined solely by static attributes.
A policy layer enables practical deployment of IEPP in real-world systems.
Key requirements include:
multi-proof authentication options
continuous authentication capability
automatic alert and reporting triggers
canonical lineage governance structures
hardware trust anchors
public verification layers
IEPP can therefore be considered a candidate architecture for trust infrastructure in AI-native environments.
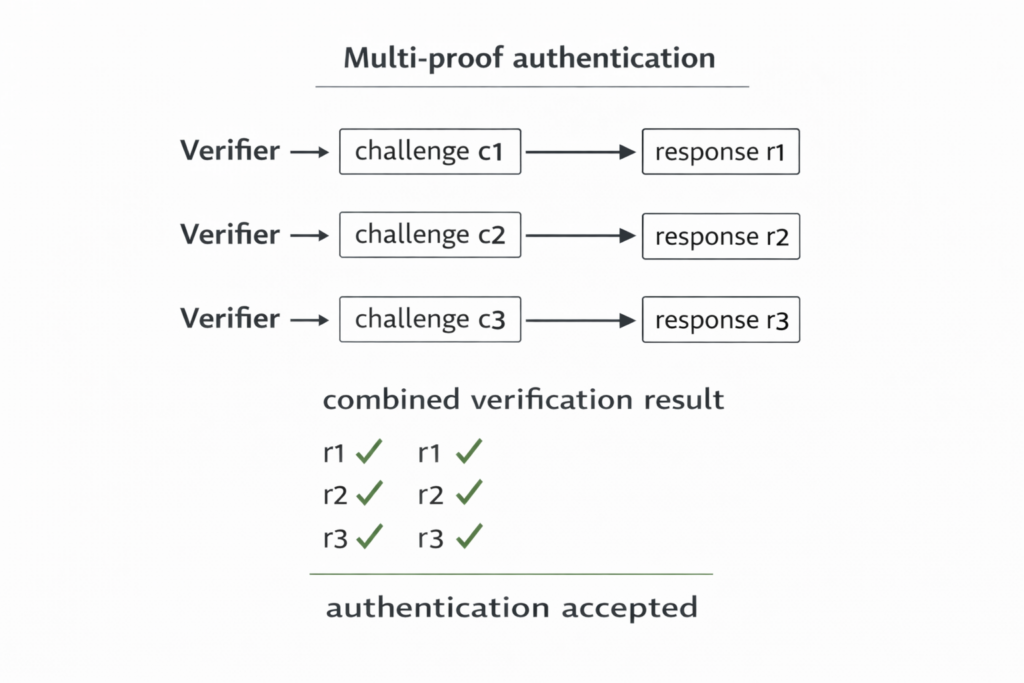
2. Multi-proof Authentication
Traditional authentication often relies on a single challenge-response interaction.
IEPP allows multiple sequential challenge-response steps to be used as part of the authentication process.
Example configurations:
3-step verification
5-step verification
n-step trajectory verification
Advantages:
increases difficulty of maintaining clone synchronization
reduces probability of replay success
increases trajectory consistency requirements
improves confidence in continuity verification
Multi-proof authentication transforms identity verification from a single point-in-time snapshot into a trajectory verification process.
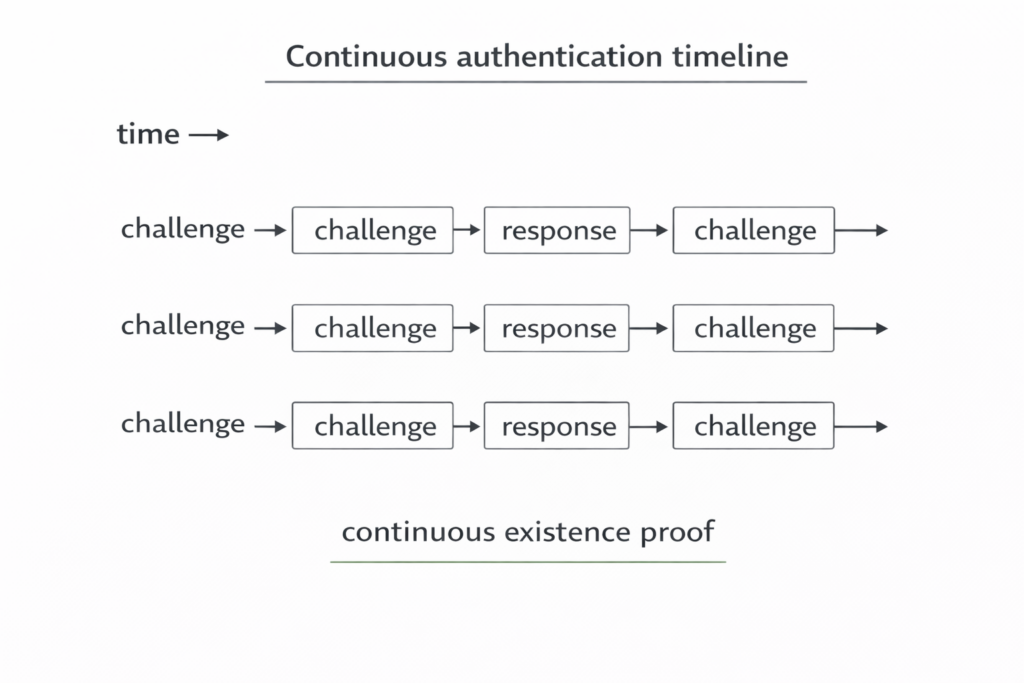
3. Continuous Authentication
IEPP supports periodic or continuous verification of existence continuity.
Possible use cases:
continuous verification after login
verification during AI agent execution
long-duration session integrity monitoring
runtime integrity validation
Continuous authentication enables detection of divergence events during operation rather than only at initialization.
Advantages:
detects clone divergence in real time
reduces impact of session hijacking
supports persistent identity continuity monitoring
Continuous verification aligns with the concept that identity is maintained through time.
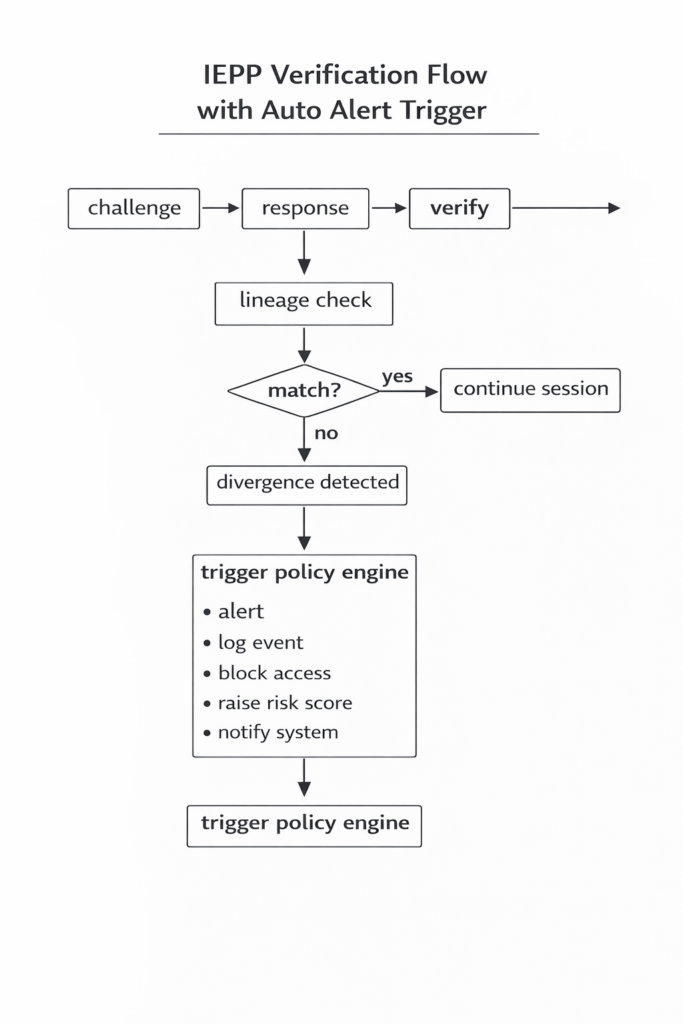
4. Automatic Alert and Reporting Triggers
IEPP divergence events can be used as triggers for automated policy responses.
Possible trigger conditions:
canonical lineage mismatch
unexpected trajectory divergence
replay detection
non-monotonic state transitions
abnormal entropy characteristics
Possible automated actions:
generate alert events
block access attempts
increase risk score
log security incidents
notify monitoring systems
trigger protective account states
Example policy behaviors:
terminate session upon divergence detection
require additional verification upon repeated mismatch
escalate security level upon anomaly detection
generate audit records automatically
IEPP can therefore function as both a verification mechanism and a trigger source for security orchestration.
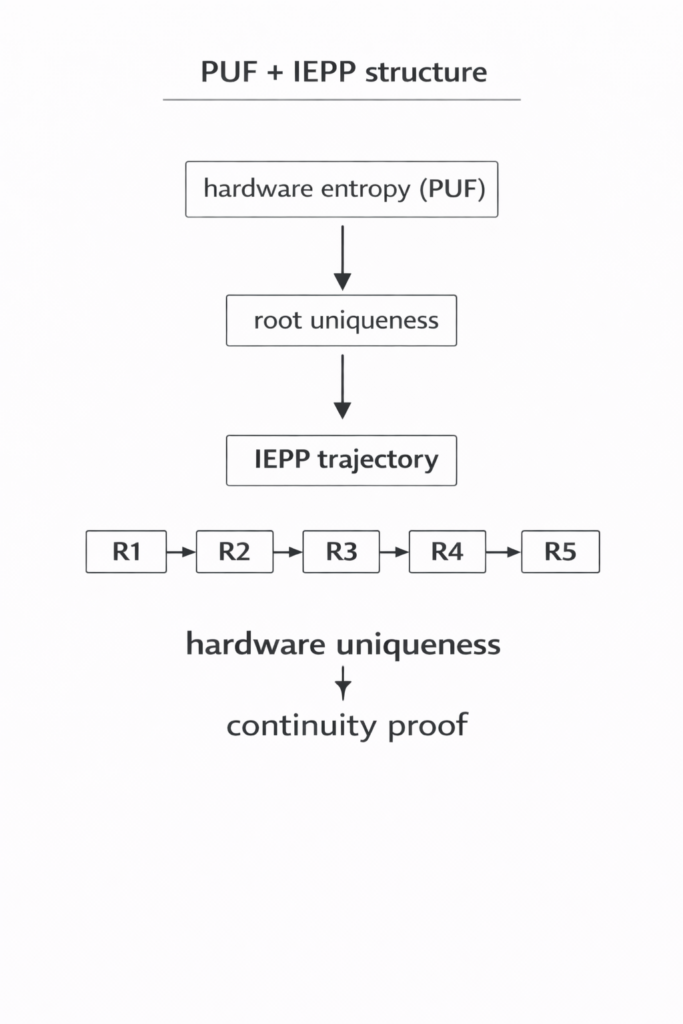
5. Synergy with PUF (Physical Unclonable Function)
PUF technologies provide hardware-level uniqueness derived from manufacturing variation.
Properties:
physically difficult to clone
device-specific entropy source
IEPP and PUF can provide complementary roles.
PUF:
provides root uniqueness anchor
IEPP:
provides continuity of identity through time
Combined structure:
hardware uniqueness + trajectory continuity
Potential advantages:
stronger resistance to cloning attacks
hardware-rooted identity continuity
additional entropy sources
6. Relationship with Blockchain or Public Ledgers
IEPP does not require blockchain in order to function.
However, distributed ledgers may optionally provide:
public auditability
tamper-evident logging
canonical lineage anchoring
dispute resolution support
Blockchain may therefore serve as an optional transparency layer rather than a required component.
IEPP remains functional without reliance on blockchain infrastructure.
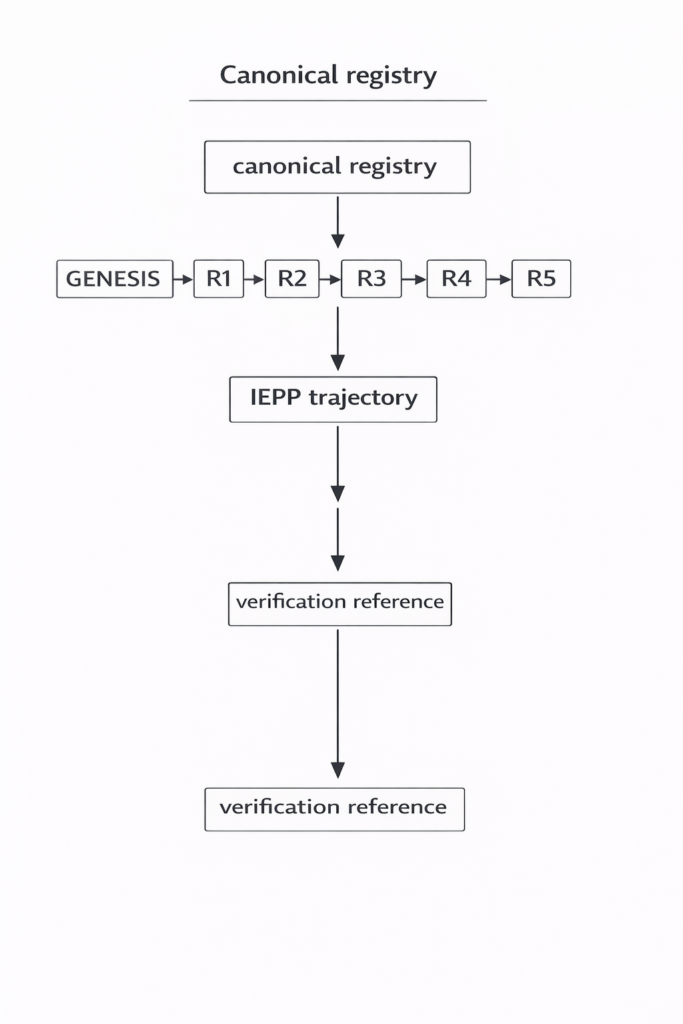
7. Canonical Registry Concept
A canonical registry may act as a reference point for trajectory continuity.
Possible roles:
store canonical lineage anchors
support divergence comparison
provide identity continuity references
assist dispute resolution
Possible architectures:
centralized registry
federated registry
distributed registry
A canonical registry functions similarly to a digital title registry.
Its purpose is to provide a consistent reference point for continuity evaluation.
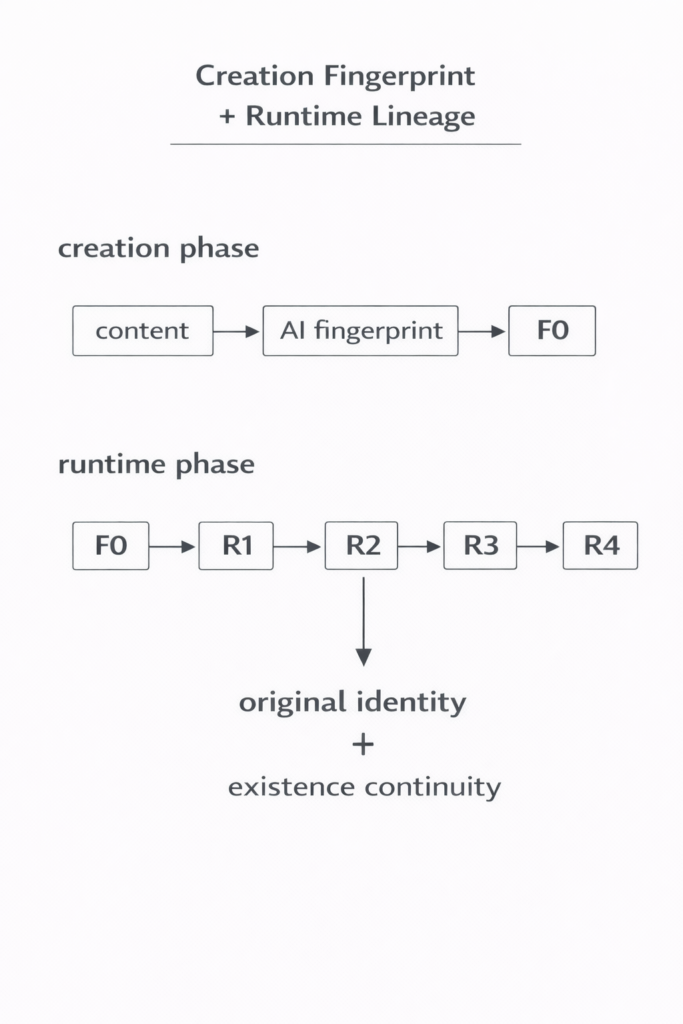
8. Integration with AI-generated Fingerprint Methods (Preview)
Ongoing research explores combining IEPP with AI-generated intrinsic fingerprint structures.
Possible structure:
creation-phase fingerprint establishes origin anchor
runtime entropy lineage establishes continuity proof
Potential result:
origin identity + continuity identity
This combination may support both:
verification of originality
verification of continuous existence
This section references ongoing work not fully disclosed in this document.
9. Multi-layer Trust Stack
IEPP may function as part of a layered trust architecture.
Example structure:
Layer 1
challenge-response binding
Layer 2
trajectory continuity linkage
Layer 3
statistical anomaly detection
Layer 4 (optional)
hardware entropy sources
Layer 5 (optional)
public audit infrastructure
Different environments may choose different combinations of layers.
The layered structure allows flexible deployment depending on security requirements.
10. Open Questions and Future Work
Several questions remain open for future research and policy development.
Who defines canonical lineage in distributed environments?
How should canonical continuation be selected when forks occur?
How should offline systems maintain continuity?
What balance should be maintained between privacy and auditability?
How should false positive divergence detection be handled?
What standard interfaces should be defined for AI agents?
How should hardware entropy sources be standardized?
How should runtime lineage integrate with creation fingerprint identity?
How should automatic alert thresholds be calibrated?
IEPP is intended as a foundation for further exploration rather than a finalized standard.